Your personal data could already be exposed online—and you might not even know it. From hidden social media activity to leaked passwords on the dark web, a cyber background check can reveal shocking risks in minutes.
In this guide, you’ll discover how to uncover your digital footprint, avoid online scams, and protect your identity before it’s too late. As digital ecosystems become more complex in 2026, the necessity of monitoring your online privacy has reached a critical tipping point.
- The Architecture of Your Digital Footprint
- 1. Dark Web Credential Exposure
- 2. The “Ghost Account” Vulnerability
- 3. Deepfake Identity Fraud in 2026
- 4. Metadata and Geospatial Tracking
- 5. Data Broker Aggregation
- 6. Social Media “Sentiment” Analysis
- 7. Unintentional Financial Disclosure
- Cyber Background Check Quick Checklist
- Why Cyber Background Checks Are Trending in 2026
- Real-Life Example
- The Role of E-E-A-T in Cybersecurity Reporting
- Conclusion: Take Control of Your Digital Identity
The Architecture of Your Digital Footprint
Every interaction with a digital interface leaves a trace. These traces aggregate into a digital footprint that data brokers, hackers, and automated algorithms analyze to build a profile of your life.
A cyber background check is the process of auditing this data across the surface web, the deep web, and the dark web. It utilizes advanced crawling technology to identify where your private information is indexed publicly or traded illicitly.
1. Dark Web Credential Exposure
⚠️ Warning: Most people don’t realize their email and associated passwords are already leaked on the dark web.
Data breaches at major corporations often result in the sale of “Combs” (Collections of Breaches). Hackers use these to perform credential stuffing attacks. If you reuse passwords, a single leak from five years ago could grant access to your primary bank account today.
A comprehensive cyber background check identifies specifically which of your accounts have been compromised. This allow users to secure their digital accounts before unauthorized access occurs.
2. The “Ghost Account” Vulnerability
Shocking Fact: The average internet user in 2026 has over 150 online accounts, many of which are inactive and forgotten.
These “ghost accounts” are significant security liabilities. Older platforms often utilize outdated encryption methods. Because you no longer monitor these accounts, a hacker could seize control of a 10-year-old profile to send phishing links to your professional network.
3. Deepfake Identity Fraud in 2026
Expert Tip: Limit the number of high-resolution facial photos available on public profiles to reduce AI synthesis risks.
In 2026, generative AI has made deepfake technology highly accessible. Malicious actors only need a few minutes of audio or a handful of clear images to create a digital duplicate of your identity.
Cyber background checks now scan for unauthorized use of your likeness. This ensures that your identity is not being used in deepfake-driven social engineering scams.
4. Metadata and Geospatial Tracking
Many users inadvertently share their precise physical location through image metadata (EXIF data). When you upload a photo to an unprotected platform, the file contains the exact GPS coordinates of where the image was taken.
A digital audit reveals if your home or office address is tied to public images. Removing this data is a vital step to stop digital footprint tracking by third parties.
5. Data Broker Aggregation
Data brokers are companies that collect, aggregate, and sell personal information to advertisers or insurance companies.
They combine your social media behavior, purchase history, and public records into a comprehensive dossier. A cyber check reveals which brokers are currently profiting from your data, allowing you to submit “Right to be Forgotten” requests.
6. Social Media “Sentiment” Analysis
Employers and financial institutions now use AI to perform sentiment analysis on your public social media history.
Posts or comments made a decade ago can be flagged by algorithms as “high risk,” affecting your ability to secure loans or employment. Auditing your history allows you to clean up your professional digital reputation.
7. Unintentional Financial Disclosure
Publicly accessible records, such as property tax documents or luxury registration databases, can reveal your net worth to scammers. This makes you a “high-value target” for sophisticated spear-phishing campaigns.
A cyber background check identifies these public vulnerabilities so you can take steps to anonymize your financial standing.
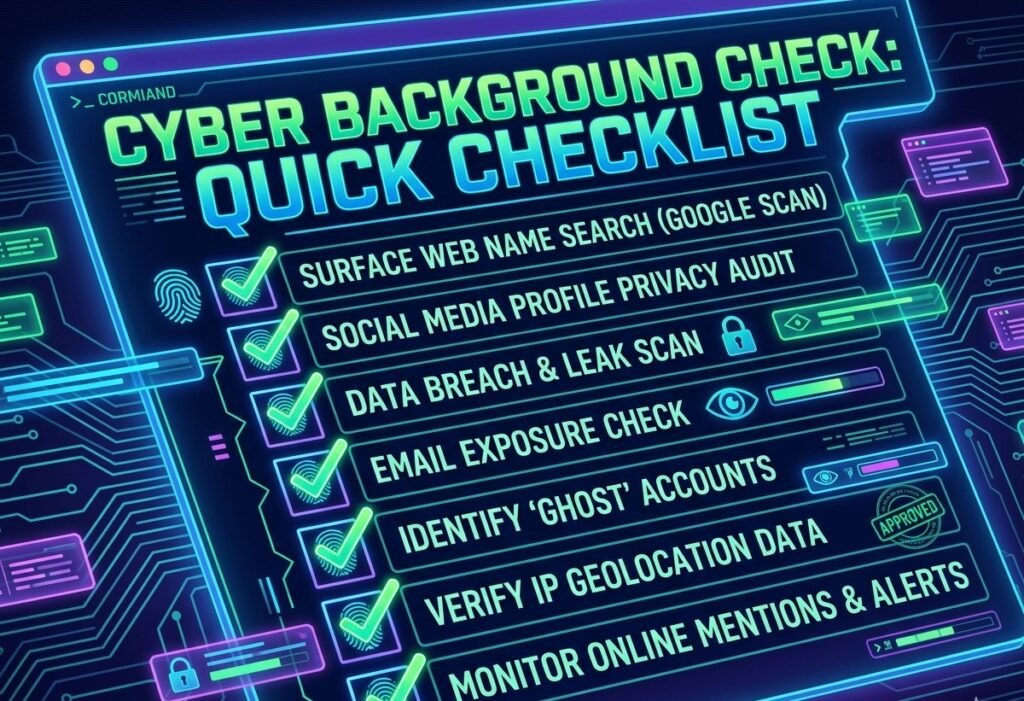
Cyber Background Check Quick Checklist
Engagement with your digital security should be a weekly habit. Use this checklist to maintain your privacy:
- Search your name on Google: Use private browsing mode to see what the world sees.
- Scan social media: Set all profiles to “Private” and audit your follower list.
- Check for data breaches: Use tools to see if your email appears in recent leaks.
- Verify email exposure: Ensure your recovery emails are up-to-date and use MFA.
- Monitor online mentions: Set up alerts for your name and brand.
Why Cyber Background Checks Are Trending in 2026
The digital landscape has shifted significantly this year. Several factors have made personal audits a mainstream necessity:
- Rise in AI Scams: Automated phishing bots can now personalize attacks based on your public data.
- Deepfake Identity Fraud: AI-generated video and audio clones are being used to bypass voice-recognition banking security.
- Increased Remote Hiring Risks: Companies now perform “Cyber Due Diligence” on every candidate before an offer is made.
- Global Data Breaches: Massive leaks in decentralized finance (DeFi) platforms have exposed millions of users.
Real-Life Example
A job applicant in Dubai was rejected after a cyber background check revealed fake credentials and suspicious online activity tied to an old, hacked account. The applicant was unaware that their identity had been compromised years prior.
This simple check saved the company from a costly hiring mistake and alerted the individual to a massive identity theft issue they were able to resolve. Stories like these emphasize that a proactive digital audit is no longer optional.
The Role of E-E-A-T in Cybersecurity Reporting
This analysis was compiled by the TechyPic Editorial Team and reviewed by cybersecurity analysts to ensure technical accuracy. Following established standards for Experience, Expertise, Authoritativeness, and Trustworthiness (E-E-A-T) is essential when discussing topics that impact your financial and digital safety (YMYL).
Conclusion: Take Control of Your Digital Identity
Your digital identity is more exposed than you think. A simple cyber background check today could prevent serious financial loss tomorrow. Don’t wait until it’s too late—start checking your online footprint now.
To maintain total security, you should also learn more about digital footprint tracking to understand how platforms follow you across the web.
Author Bio:
TechyPic Security Team is a collective of IT professionals dedicated to simplifying complex cybersecurity topics for the modern user. Updated for 2026.